We want to come together to exchange ideas, make new friends, and build things as an inclusive community set adrift on the high digital seas, navigating these distributed networks by no more than the stars in our own eyes.
Hackers and pirates care about code; not criteria such as degrees, age, race, nationality, sex, sexual orientation, gender, gender identity or expression, disability, physical appearance, religion (or lack thereof), or position.
Be Open
Be welcoming to all. Especially welcome newcomers to the community. Great things can happen when we show up with an open mind and curiosity.
This also refers to the fact that all code submitted to this repo for consideration at the hackathon must be open source. We use the Mozilla Public License most often at Status, but you can find a good list of options here
Be Kind
Be kind to others. Treat their work, time, and perspectives as worthy of your attention. Treat others as you would like to be treated yourself and respect the #buidl.
Express Yourself Freely
Dare to create something nobody has before. Code counts more than words, so come and be your most radical self at all levels of the stack.
Build Stuff That Matters
We're here to bring crypto closer to life, so pay attention to the world around you, rather than the passing promise of riches or fine booty. Make public data available, protect private data. Build what matters to you. You can create new applications, find/fix bugs & vulnerabilities, work on bounties, or help others during their hacking. You can create art and beauty on a computer: a whole cosmos awaits.
Hacking Starts at #CryptoLife
Hacking starts during the event. Teams can form and ideas can evolve before the hackathon. However, the code base, hacks, and prototypes that you submit for prizes or bounties need to be written during the event itself. Apps, hacks, and projects that were built before the event do not qualify and will be excluded from judging and any prizes.
Bugs & Vulnerabilities
If you believe you have found a bug or vulnerability, please submit a report to the appropriate team or project right away. Make a good faith effort not to access or destroy another user's data. Act for the common good through the prompt reporting of all found vulnerabilities. Don't willfully exploit others without their permission.
Inspiration Drawn From
- ETHBerlin Code of Conduct
- Hack Code of Conduct
- Berlin Code of Conduct
- CCC Hacker Ethics
- Hacker One Disclosure Guidelines
- Steven Levy’s Hacker Ethic
Contact
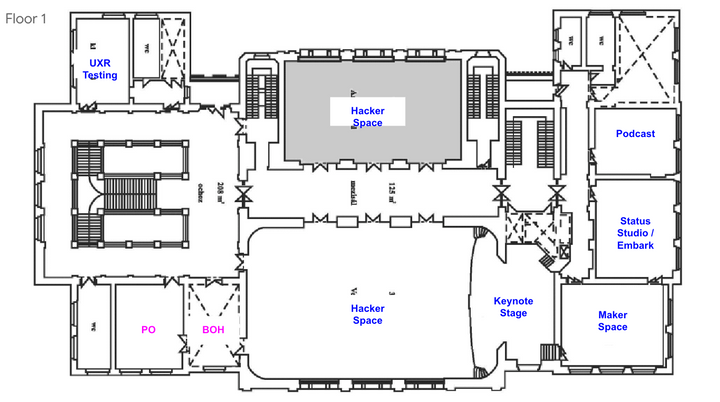
If you have any questions, before or during the event, please contact ceri@status.im or find her in person (it's pronounced K-er-y) at #CryptoLife for all your pirate needs.
Additional rules
No striking one another on board, but every human's quarrels to be ended on shore, at sword and pistol. The quarter-master of the ship, when the parties will not come to any reconciliation, accompanies them on shore with what assistance he thinks proper, and turns the disputants back to back, at so many paces distance; at the word of command, they turn and fire immediately (or else the piece is knocked out of their hands). If both miss, they come to their cutlasses, and then she is declared the victor who draws the first blood.
To desert the ship or their quarters in battle, is punished with death or marooning.