The security audit by Trail of Bits (ToB) of the Status Mobile App for the V1 release is done, let’s talk about it! Zero (0) critical issues found and less than forty (40) total issues identified.
What we wanted to do
We’ve been hard at work trying to get the Status Mobile App to a state where we feel it is ready to put the big 1.0 version number on it. Before we were comfortable doing that, we needed an updated security audit on the codebase. The Beta release had been previously audited by Deja Vu and there has been a lot added and changed since then; we need a different set of eyes to double and triple check our work for potential issues. To that end, we contracted Trail of Bits for a nine (9) person-week engagement with four (4) engineers to cover as much of the code as possible with a focus on high-risk elements of the Status mobile application in the following repositories (in order of priority):
That’s a lot to cover in nine person-weeks! The engagement goals were as follows:
- Is it possible to take down the Status network with little effort?
- Is the privacy of messages respected?
- Can an attacker send undesirable messages?
- Does Whisper achieve its security goals?
Their methodology was a combination of manual code review and automated testing, including building harnesses for fuzzing and fault injection for the various repositories.
How it went
Overall, we are quite pleased with the results of the audit. Trail of Bits found no critical issues and less than 40 total issues of which the Status team is already fixing.They not only identified issues within the codebase but also identified deeper design issues and made recommendations to fix some of the behavior that led to them. This is vastly more valuable to us, as it helps Status develop a more secure and stable codebase over the long term.
The ToB team went to work and quickly started finding issues after getting acquainted with the codebase. Specifically, the final report had the following Severity and Category breakdowns:
| ||||||||||||||||||||
|
All issues were reported both via a final report and GitHub issues, each issue complete with severity/difficulty attributes, a description, exploit scenario, and short/long term remediation recommendations. These issues will be available for public consumption and review after a choice set of issues have been remediated.
What we’re going to do
Our plan from here is to address every issue that was brought up by the ToB team. As for V1, due to time constraints, we are going to select the most critical issues that result in a direct impact on user experience or loss of security and fix them before the V1 launch; scheduled for early January.
After V1 launches, we plan to tackle the rest of the issues raised diligently. Some of the features and improvements we are currently working on already address issues found, but aren’t scoped for the V1 release; That means they’ll be fixed when the feature or enhancement is incorporated into the Status Mobile App.
Outside of fixing the issues reported, we will be spending a good amount of resources and time setting up and using the frameworks provided by ToB during their automated analysis - e.g. continuously fuzzing and fault-injecting our application to look for bugs our current testing does not catch. This will allow us to continue the work they started and build a more secure software development lifecycle. It is clear from the category breakout of issues that Data Validation is a problem we have in our development lifecycle, and these endeavors should drastically improve that.
A great additional benefit of an external audit is an evaluation of the current documentation. The assessment team can be thought of as new employees trying to get up-to-date on how things work as fast as possible, which means they’ll be relying on your documentation heavily. The process of discussion throughout the audit between Status and ToB identified weaknesses in our documentation and specifications of how Status works. To this end, we will be applying additional efforts to shoring up the hang-ups ToB experienced as well as looking into why they existed in the first place.
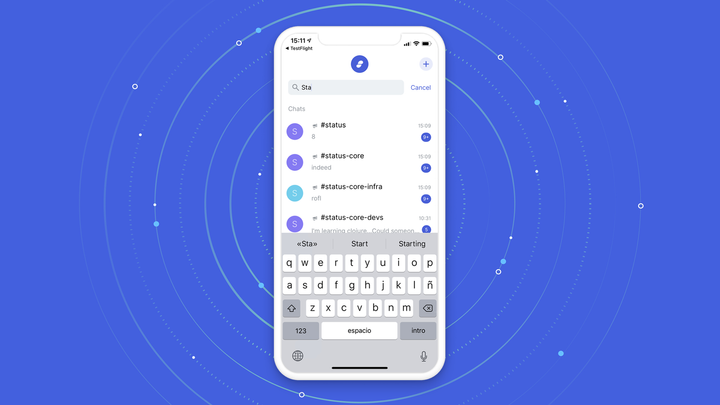
Get Status
You can grab the latest beta version of Status for iOS and Android. Test it out before the v1 launch coming soon!
iOS
- Within TestFlight, make sure you see version 0.12.0 and tap ‘INSTALL.’
- If you don’t currently have Status installed, access via TestFlight here: https://testflight.apple.com/join/J8EuJmey.
Android
If you are not automatically asked to update, go to Status.im in the PlayStore and click ‘Update.’
For more information, please join us in Status or the Status Discussion Forum