Expanding on security efforts through bug bounty programs, rigorous auditing, education, and open source contribution. Learn more about the ways Status is increasing security efforts ahead of the public release.
As we approach the official production release and begin to deliver on SNT utility within the application via features such as Tribute to Talk, Network Incentivization, Sticker Market, and the Teller Network, it is imperative that user security is at the core of our efforts and is not compromised.
After all one of our core principles is:
Security – We don’t compromise on security when building features. We use state-of-the-art technologies, and research new security methods and technologies to make strong security guarantees.
Status aims to be a truly decentralized communication tool – eventually removing all third parties including services such as Infura. In doing so, Status can minimize the attack vectors for malicious actors leaving the end user in total control of their web3 experience. However, it is important to note that with greater freedom and control, comes additional responsibility. The removal of trusted third parties places the ownership of responsibility entirely on the user. It is thus Status’ responsibility to provide these features in an available and intuitive way so that the user can make responsible and informed decisions.
One of the true benefits of web3 is the ability to transact and communicate on our own terms – without middle men. In order to enjoy this type of free communication, we must be confident that our messages, transactions, identities, and funds are safe and secure.
Bolstering the Security Effort
In October 2018, Dr. Corey Petty joined Status as Lead Security Engineer. Under this role, he is responsible for ensuring the overall security of the application including the smart contracts involved, user transactions, and general security education.
Corey holds a PhD in computational chemical physics with a specialization in exact quantum dynamics. After a post doctoral study, he left the academic world to pursue the intersection of blockchain and security. He spent some time in the security consulting industry working for Novetta Solutions and an elite cybersecurity research division of Booz Allen Hamilton, Dark Labs. There he worked to educate others on how blockchain networks work in detail as well as develop novel solutions to existing problems in cybersecurity, mainly in the industrial control systems industry. Corey has also had the opportunity to have a multitude of in-depth conversations with thought leaders since his co-founding of The Bitcoin Podcast Network in 2015. All of this has fueled and directed his ongoing research to learn and understand the fundamentals of this technology and the people behind it.
To contact Corey, you can reach him directly on Status or within the Status Security Channel #status-security.

What Does Secure Communication Mean for Status?
We agree with the 2018 Secure Messaging Series by the EFF – secure messaging can mean many different things depending on whom you ask. To some it means reliable messages in resource restricted devices and areas of low connectivity. To others, it means privacy from government surveillance and minimal leakage of metadata. Secure messaging is certainly not one size fits all.
Web3 technology has taken this a step further with the removal of trusted intermediaries and the introduction of digital currencies. Cryptocurrencies and financial transactions within applications like Status have introduced an entirely new layer to “secure messaging”.
The Status Mission is “[to become] a secure communication tool that upholds human rights. We enable community money, community law and through privacy, preserve culture."
To be considered a truly secure communication tool, we are committed to ensuring the following:
- Secure Messaging - messages are not censored, blocked, and they remain anonymous if the end user chooses so. Only intended recipients are able to view messages and no metadata is leaked.
- Secure Financial Transaction - sending, storing, and receiving cryptocurrencies or tokens within the Status wallet is safe from attack. Private keys are never exposed. Transactions are only processed when initiated and confirmed by the owner of the private keys.
- Secure browsing - when browsing web3, end user data and browsing information is not accessible by any third parties. Any transactions made while using the Status browser implement the same security standards and best practices used in the Status wallet.
Technical Implementations
Status leverages state of the art technology to ensure the highest level of security possible. Many of these technologies are under constant R&D, and Status is working alongside many web3 teams to push these protocols and standards further, making them more secure, more reliable, and scalable.
At a technical level, here are some of the security implementations in the product:
- Whisper Protocol - p2p gossip protocol used for sending and receiving messages. Whisper messaging aims to deliver “darkness” via multicast dark routing. Further details on whisper here.
- Perfect Forward Secrecy - a feature of specific key-agreement protocols which provide assurances that your session keys will not be compromised even if the private keys of the participants are compromised. Specifically, past messages cannot be decrypted by a third-party who manages to get a hold of a private key. Details on PFS here
- Browser privacy mode enabled by default - this means that DApps will be required to ask permission before connecting to your wallet, and it may cause some DApps to break.
Status has also introduced Keycard as an additional layer in protecting your private keys and crypto transactions.
Decentralized Account Creation
One of the key security features of Status is the removal of features all together. Meaning, when one installs and creates a new account on Status, it is done entirely without the use of third party verification.
No email. No phone number. No connecting a social media account. When a new account is created, it is simply the user and the keys generated with the True Random Number Generator. This completely removes the threat of attack via third party credentials.
Keys are stored on the user’s device alone (as opposed to a third party data server in third party location).
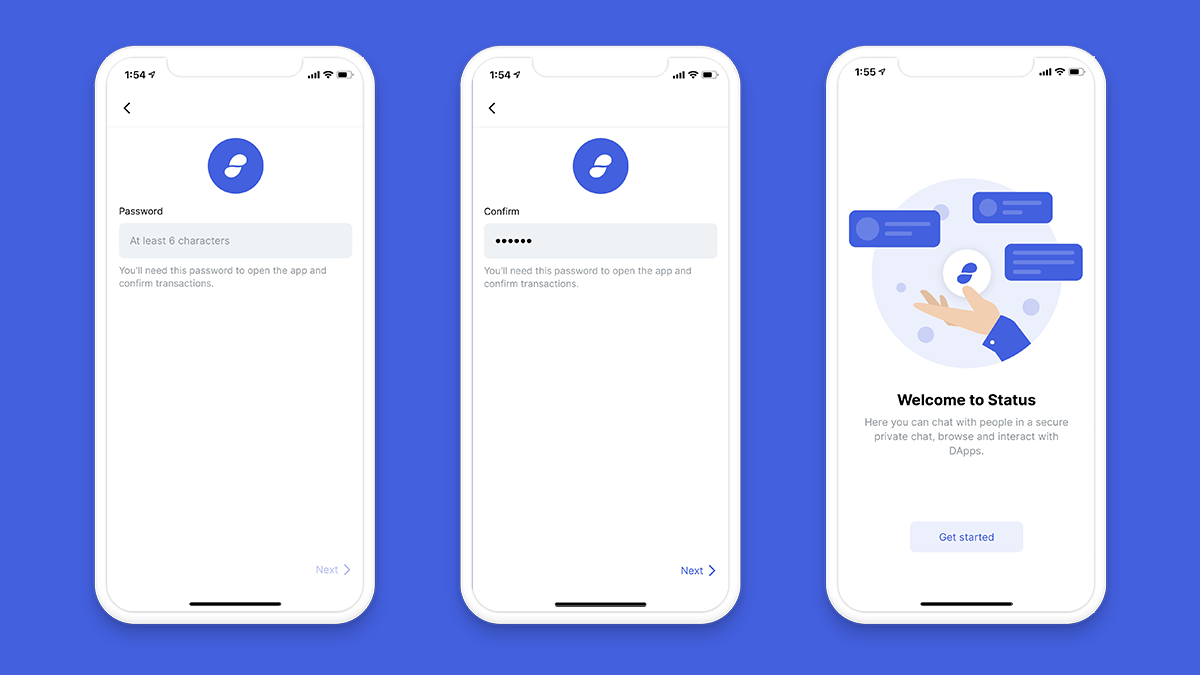
Designing a Security-first UX
Web3 security goes well beyond the technical implementations in the codebase. With responsibility placed in the hands of the owner of private keys, it is crucial that the user experience and app interface are intuitive, clear, and preventative. Therefore, it is our goal to create an experience that is simple yet provides enough information to allow the user to make well informed, confident actions.
This requires added layers of security at the interface level to ensure end user education as well as anti-phishing procedures. Some of these features include a well researched and tested onboarding experience as well as the introduction of the signing phrase.
Rigorous Auditing
Before we can feel comfortable releasing a secure version of Status, we want to ensure the code and associated smart contracts are audited by capable, trusted, and well respected third parties.
Since joining, Corey formed lasting relationships with the top auditing firms in blockchain security. He participates in discussions with the ETHsecurity community to stay abreast of best practices and guidelines being developed, as well as new research and breaking security issues. Moreover, Status has entered into a long-term retainer agreement with Trail of Bits to provide additional professional security resources across Status development where needed.

Status takes a stance of evaluating all features and functionality in terms of overall risk, and then allocating the appropriate resources to ensure they function as intended. To this end, we aim to stay compliant to community standards and guidelines given by the ETHsecurity organization.
Proper security review is currently planned and in place for all features with smart contracts associated. This includes:
- ENS naming system
- Tribute to Talk
- Sticker Market
- Teller Network
- Dapp Store Curation Market
All audit results and findings will be shared publicly as was done ahead of the beta release in June 2018.
Bug Bounty Program
The beauty of free and open source software is the added security associated with constant scrutiny, review, and improvement. All of our code is entirely open source and available on Github.
With that, we are planning a public Bug Bounty Program with one of the most highly trusted security platforms in the industry – Hacker One. Hacker One has conducted bounty programs and security programs with organizations such as Shopify, Airbnb, Spotify, The United States Department of Defense, The European Commission, and Twitter.

Details of the Bug Bounty Program will be shared once all final details around scope and bounty payouts are finalized. For more info:
Join the Status Security Channel: #status-security
Check out and star the repo’s: status-react & status-go
Ongoing Monitoring of Infrastructure
Often much of the security focus is placed on the preparation and development of features and infrastructure, and then lacking afterwards. Status is spending a lot of effort here as well.
Even though our goal is to minimize the required infrastructure to run Status, we take the responsibility of what we do deploy very seriously. To help us continuously monitor our infrastructure, Status has employed the help of Threatstack, a leading cloud security firm. This engagement has also helped inform traditional security firms how to think about decentralized organizations like Status and has been very fruitful.
We have also been formalizing the process for monitoring and response of incidents with deployed smart contracts. It is not enough to deploy a smart contract and assume it works as intended, and Status is actively working with security leaders to improve the monitoring and alerting of undesired activity of blockchain assets. For more info, join #status-security in Status.
Best Practice
As stated above, the more we decentralize the technology, the fewer intermediaries we rely on. With fewer third parties, the greater responsibility we all take on as users and holders of our private keys.
Therefore, a major effort of Corey and the Status Security team (and blockchain community at large), is to educate the world on how to secure yourself and take responsibility for your keys, funds, and general online safety.
Check out and contribute to the Security Best Practice document here. This includes everything from how to store your private keys, how to avoid phishing attacks, and recommendations for offline cold storage and hard wallets.
Get Involved:
We at Status are not limited to the activities outlined in this post, and are always looking for great ways to improve the security of our organization and applications. If you know something we don’t, please reach out and talk to us!
Status Security Channel: #status-security
Contact Corey Petty: corey@status.im, or in Status (petty.stateofus.eth)
Github: https://github.com/status-im
Best Practice Doc: https://notes.status.im/Fa9h9kCVRtm82PcgQ31Y7w