Abstract
Pseudo-anonymity enables an open society.
Privacy is a basic human right and a requirement for true self-expression, free flow of information, and autonomy. Total anonymity is not always a realistic goal for a functioning society as proof of ownership and right to access requires some proof of identity and or reputation. However, pseudo anonymity enables the right to privacy for one’s real self while enabling the “right to access” and reputations as social currency. Separation of identities across our real selves, our social selves, and our earning self, can provide privacy as well as right to access.
The article will make the case for pseudo-anonymity as a requirement for an open society.
Introduction
Privacy is a basic human right. Not only does it protect people from oppression and persecution, it enables the free flow of information, self expression, and true individual autonomy. However, centralized intermediaries across our transactions and social networks have been steadily eroding privacy and security from modern society.
Intermediation does have its benefits such as efficiency and convenience. Third party intermediaries can also protect people from fraud, identify illegal activity, and serve as trusted arbiters. More importantly, intermediaries support “the right to access” – meaning the ability to prove things such as ownership, citizenship, and value. However, they often require people to give up significant amounts of personal information, rendering privacy nearly impossible within given systems.
The introduction of blockchain technology, peer-to-peer and distributed systems, and advanced forms of encryption have removed the requirement of third parties. These technologies allow people to transact with one another in a peer-to-peer manner, and in some cases, even allow for total privacy.
While privacy is a basic human right and a requirement for true self-expression, free flow of information, and autonomy; total anonymity is not a realistic option for a functioning society. However, pseudo-anonymity can enable the right to privacy for one’s real self while enabling the right to access and reputation via constructed selves, or “pseudonyms”. Using the advanced technologies stated above, individuals can create pseudonyms and have private identities across our real selves, our social selves, and our earning selves, all while maintaining the right to access.
The article will make the case for pseudo-anonymity as an enabler of an open society.
Privacy as a Requirement of Autonomy
Privacy is a basic human right – and one that is a requirement for individual autonomy. According to the United Nations Universal Declaration of Human Rights:
“No one shall be subjected to arbitrary interference with his privacy, family, home or correspondence, nor to attacks upon his honour and reputation. Everyone has the right to the protection of the law against such interference or attacks”
Studies show that when someone knows they are being watched, they act differently, which can be seen as a loss of self expression. Simply put, surveillance (lack of privacy) may cause people to change their behavior and become conformists. (McSweeney's issue #54: "The End of Trust.")
The idea of conformity via surveillance is well put by Glenn Greenwald in his 2014 Ted Talk:
“[By giving into surveillance] I have agreed to make myself such a harmless, unthreatening, uninteresting person, that I actually don't fear having the government know what it is that I'm doing.”
A lack of privacy is detrimental to not only individual autonomy, but also the progression of society as a whole. Take the example of a surveillance state in which people do not willingly express opposing viewpoints out of fear of being persecuted, incarcerated, and even worse, physically harmed.
There are a number of instances in which authoritarian governments strike fear into the public and prevent them from openly speaking their minds, taking to the streets in protest, and spreading opposing ideas.
This extends into other forms such as academia and corporations. For example, many academics will be biased by their advisors above them and will only push back so much due to fear of certain career retribution or outcasting.
Carl Ichan on corporate America is a good example comparing the current structures to Feudalism instead of democracies. In these instances the CEO or Chairman sets policy in most cases and everyone under them makes sure to comply with the person above them or fear for their job. As managers leave or retire it leads to a devolving cycle of promoting yes men – a culture where people are disincentivized to speak their minds. Now imagine an organization where everyone can voice their opinion and participate in the governance without fear of this retribution.
The Right to Access
Just as privacy is critical to an open society, the “right to access” is required for a functioning society. The right to access is the ability to prove one’s ownership of value, credential, or even clearance to specific digital and physical spaces.
The right to access and prove ownership is critical for individual autonomy. For example, the ability to prove ownership of property must be tied to a specific identity. In a completely anonymous situation, there would be no possible way to associate ownership of property between two seemingly identical identities.
The right to access can also be applied to how we manage our funds and bank accounts. Without the ability to prove ownership, our individual value would be free for any anonymous actor to gain access to. I need the ability to prove what is mine from what is yours.
Another example is the ability to prove citizenship to states. In today’s society, most people hold passports to specific states, granting them the right to access various borders. The opposite is seen for individuals who do not hold required documentation proving access to a specific country or state, oftentimes leaving the person in question stateless.
Not holding proof of nationality—being "undocumented"—is not the same as being stateless, but the lack of identity documents such as a birth certificate can lead to statelessness. Many millions of people live their entire lives without documents, without their nationality ever being questioned. The United Nations Children's Fund (UNICEF) estimated in 2013 that 230 million children under the age of 5 have not been registered – meaning they cannot prove right to access specific states.
It should be possible to maintain the basic human right to privacy, while still holding the right to access and prove ownership. This is done through various levels and types of identification made much more accessible through distributed systems and advanced forms of technology. What if a single person or entity could create and maintain unique pseudonyms which grant access to distinct things.
The Right to Access & 3 Types of Identity
As mentioned above, individuals must be able to successfully prove right to access - therefore true anonymity is not a viable option for a functioning, open society and autonomous individual. Anonymity is to be without any name, lacking individuality, unique character, or distinction. By definition, it is impossible to obtain both anonymity and right to access.
Anonymity can be seen as the ultimate form of privacy. In fact, it is used in free elections by law to protect the identity of the voter. In this case, no name or identity is tied to a ballot, rendering it impossible to tie the right of ownership of a specific vote, to a specific identity. This prevents coercion as well as retaliation against an individual for an opinion. Anonymity is also seen in forums such as 4chan - where nameless, unidentifiable entities can comment and communicate without fear of exposing any identity at all (although IPs are now potentially traceable). These forums have been used to spread internet memes, coordinate activist and political movements, as well as converse in illegal, racist, and harmful activities.
Anonymity is difficult to achieve and is often fraught with legal issues. True anonymity requires unlinkability, such that an attacker's examination of the pseudonym holder's message provides no new information about the holder's true name.
The other end of the spectrum is leveraging a real identity associated with a real person across varying areas as right to access. This is widely seen today via things such as government issued identification – passports, birth certificates, drivers licenses, etc. These forms of identification not only include information about or right to access a specific state, but also often include information about our age, location of birth, appearance, where we have been, biodata in fingerprints and retina scans. While these forms of identification are required by law for things like international travel, why are they used for job applications, buying a home or car, and applying for a bank account? Leveraging a real identity across varying levels of proof leaves true privacy impossible.
The third type of identity, is a pseudonymous identity. One in which a moniker or assigned name is used in a given context. Pseudonymous names are able to persist through time and even build reputations, right to access, and prove-ability of ownership. A single person can create multiple pseudo identities and keep them across various channels of communication. A pseudonym is linked to a real person or entity which enables the right to access while still holding some level of privacy. Pseudonymity provides assignability while preventing character assassination.
Pseudo Anonymity can protect the real identity of the associated profile. This has many benefits in a world in which people are prosecuted, imprisoned and even physically harmed for their public views and opinions. As described by Zero Hedge. “anonymity is a shield from the tyranny of the majority. it thus exemplifies the purpose behind the bill of rights, and of the first amendment in particular: to protect unpopular individuals from retaliation-- and their ideas from suppression-- at the hand of an intolerant society."
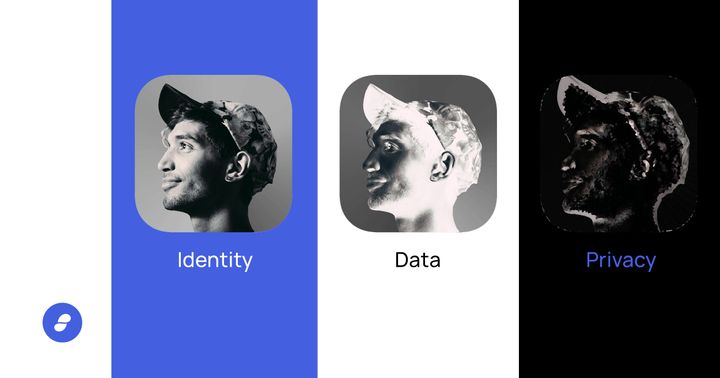
Here we have outlined three forms of identity:
- Anonymity - Unlinkable to a real identity. Impossible to prove right to access. Used in free voting and forums such as 4chan
- Real Identity - Directly linked to a real identity. Inherently proves right/denial to access. Passports, birth certificates, and government issued documents. Common on Facebook.
- Pseudo-anonymity - Potentially linkable to a real identity. Possible to prove right to access to specific things. Social channels such as twitter.
Degrees of Pseudonymity
A single entity can create multiple pseudonyms for use on various platforms. For example, a single person can have one name used on Twitter, another unlinkable name used on Reddit, and another pseudonym used in Status. While all three of the unique names are tied to a single person, they are immediately unlinkable to each other. The internet has enabled varying levels of pseudo anonymity:
- Highly linkable public pseudonyms in which the link between the pseudonym and a human being is publicly known or easy to discover. I.E many social profiles.
- Potentially linkable non-public pseudonyms in which the link is known to system operators but is not publicly disclosed.
- Unlinkable pseudonyms where the link is not known to system operators and cannot be determined.
In examining a Twitter Profile, vitalik.eth / @VitalikButerin for example, you notice that this profile is highly linkable to the real Vitalik Buterin. It is a verified account, has 900k+ followers, and links to an about.me website likely operated by Vitalik himself. While his real name and identity is Vitalik Buterin, his highly linkable twitter pseudonym is vitalik.eth. This pseudonym is provided right to access the verified blue checkmark as well as the social reputation that comes with Twitter. However, it will not grant access to a new country the same way a passport would.
Degrees of pseudonimy are well described by Arvind Narayanan with the idea of 33 bits of Entropy. With roughly 7.5 billion people in the world, you only need 33 bits of information about a person to determine who they are. 2^33 is 8.6B and there are only 7.5 billion people in the world. Therefore, with 33 bits of independent information, you can de-anonymize someone. If they have 0 bits of anonymity left, you know exactly who they are. With 10 bits of anonymity left, they are 1 out of 2^10 or 1 out of 1,024.
I have a number of bits of anonymity. Therefore anonymity is not a 1 / 0 game.
Therefore, a pseudonym will only be an unlinkable name if it can hold 32 bits of entropy. When examining the multitude of platforms we use and the amount of information gathered on each and every one of every day, 33 bits of information is not much at all.
This concept is explained by Balaji Srinivasan in his talk called “The Pseudonymous Economy”
Examples of Pseudo-Anonymity
There are many concrete examples of pseudo-anonymity in both current time and throughout history that showcase the varying degrees of pseudonym and as an enabler of open societies.
One of the most widely used pseudonymous platforms in use today is Twitter. With Twitter, anyone with an active email address can set up an account, create a pseudonym and start broadcasting their thoughts to the world. Of course, Twitter requires an email address or phone number along with a birthdate for account creation, so system administrators will be able to associate the pseudonym with the correlating email address.
When first creating an account, with no followers, without following anyone else, and with no tweets, one could maintain some bits of anonymity (assuming a false moniker is used and not one's real name). There are few public links back to the users real identity.
Then as one starts to gain followers, follow people back, and tweet about their personal opinions and maybe even identity, the pseudonym will begin to lose bits of anonymity.
The Federalist Papers
The Federalist Papers is a collection of 85 articles and essays written by Alexander Hamilton, James Madison and John Jay under the pseudonym "Publius" to promote the ratification of the United States Constitution.
In 1787 the Federal Convention sent the proposed Constitution to the Confederation Congress, for ratification of the states at the end of September 1787. This was met with large criticism in the Anti-Federalist Papers, which were also written under pseudonyms. The Federalist Papers was largely a response to the Anti-Federalist Papers by Alexander Hamilton as an extensive explanation of the proposed Constitution to the people of the state of New York. He later recruited James Madison and John Jay to help write some of the articles.
The 3 authors chose to publish their work pseudonymously in an attempt to hide their true identity. People were able to ultimately discern the true identity of the authors and place ownership to their real names.
Kalzumeus - Japanese COVID-19 Research
On March 25, 2020 a report was published under a pseudonym in attempt to raise awareness of potential misinformation about COVID-19 in Japan. The pseudonymous group had been conducting an independent research initiative to investigate the virus. In this report, the group makes note that “as of March 19th, the official statistics show less than 1,000 coronavirus infections in Japan. This compares extremely favorably with the experience of peer nations such as Italy and the United States, despite Japan’s first infections having occurred earlier.”
There was sentiment throughout the country that measures put in place such as widespread mask use and social distancing had sufficiently contained the coronavirus situation. It wasn’t until Monday April 6th that the Prime Minister announced a state of emergency will be declared in seven prefectures, including Osaka and Tokyo.
However, the group felt there was enough global evidence to support the need for stronger government action to prevent the spread of the virus.
The group worked and reported the research pseudonymously to protect the potential negative impacts to the individuals involved. It was not until April 21st that Patrick McKenzie shared the report from his personal Twitter account, revealing the person behind the report.
Bitcoin & Satoshi Nakamoto
Satoshi Nakamoto is the pseudonym of the person or persons who developed bitcoin and authored the bitcoin white paper. This is a very powerful move that has had many long term impacts on Bitcoin today.
Most notably, it protected the true identity of the person, or persons behind the work. If their identities had been revealed, they could have been attacked, prosecuted, and the work could have been shut down. It therefore protected the network as a whole.
Working under the pseudonym Satoshi Nakamoto also spoke to the ethos of the project. By assigning an identity to the work, it gives an element of empathy that there is a real person (or people) behind it. This also adds an element of tangibility to the ideas.
Bitcoin can also be seen as an activist movement or public good. By working under a pseudonym it provided a constructed identity. In an interview with Lex Fridman, Jack Dorsey stated “a pseudonym is constructed identity….the identity being built was a short time window, it was meant to stick around and to be known and it is being honored in how the community thinks about building it”
Assigning the Right to Access
Given we have the ability to create multiple pseudo anonymous identities with modern technology, social platforms, and advanced encryption, we can now assign individual rights of access to specific pseudonyms. This now means, one can have a real identity, various social pseudonyms, financial pseudonyms, etc.
To obtain true autonomy, one should be able to assign the right to access ones financial wealth to a specific pseudonym. One that is entirely separate, unlikable, and private from their twitter pseudonym.
One should be able to assign the right to access a physical, credentialed space without sacrificing their social pseudonym. The protection of a social identity is crucial for the ideas mentioned above, namely the protection of character assassination, social credit, and even physical bodily harm.
Separate pseudonyms assigned to specific rights of access achieves both privacy and ownership and is therefore critical to individual autonomy and an open society.