Privacy is a fleeting occurrence in today’s world. Our communication tools require us to reveal our true public identity, our social platforms are collecting mountains of data on us every day, and in some cases, our governments are surveilling our every step. This is why Privacy is one of the 10 Status Principles
"Privacy is the power to selectively reveal oneself to the world. For us, it's essential to protect privacy in both communications and transactions, as well as being a pseudo-anonymous platform. Additionally, we strive to provide the right of total anonymity."
This makes a strong case to create tools and infrastructure that preserve our privacy or at least give us the option to reveal our real identities in certain circumstances. In a previous article we make the argument that pseudo anonymity not only enables the free flow of information, but is actually a requirement for a truly open society.
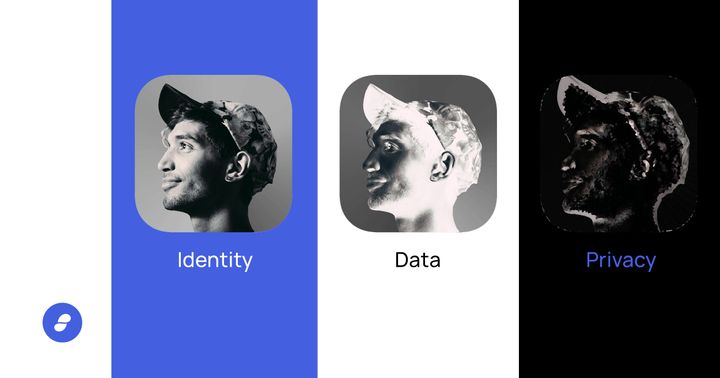
Here we will outline and recap the three forms of identity:
- Anonymity - Unlinkable to a real identity. Impossible to prove right to access. Used in free voting and forums such as 4chan
- Real Identity - Directly linked to a real identity. Inherently proves right/denial to access. Passports, birth certificates, and government issued documents. Common on Facebook.
- Pseudo-anonymity - Potentially linkable to a real identity. Possible to prove right to access to specific things. Social channels such as twitter.
Status is designed to be a pseudo-anonymous platform and we are exploring ways to introduce total anonymity.
Anonymous Identity
Anonymity can be seen as the ultimate form of privacy. An entirely anonymous identity has zero connection to a real person's real identity whatsoever. In fact, it has absolutely no identity tied to it at all.
“The important idea here is that a person be non-identifiable, unreachable, or untrackable. Anonymity is seen as a technique, or a way of realizing, a certain other values, such as privacy, or liberty.”[1]
Some examples of anonymity:
- Free elections: Anonymity is used in free elections by law to protect the identity of the voter. In this case, no name or identity is tied to a ballot, rendering it impossible to tie the right of ownership of a specific vote, to a specific identity. This prevents coercion as well as retaliation against an individual for an opinion.
- 4chan: nameless, unidentifiable entities can comment and communicate without fear of exposing any identity at all. (although this is changing with traceable IP addresses)
- Status Moot: for some time, there was a public channel in Status in which anyone had access to the same chat key. This meant that there was no way to tie specific comments back to an individual identity. All messages were sent by “moot” instead of a prescribed pseudonym
True anonymity requires unlink-ability, such that an attacker's examination of the pseudonym holder's message provides no new information about the holder's true name. This means that even so much as an IP address can mean an identity is not entirely anonymous, but rather pseudonymous.
Some people make the argument that true anonymity can reduce the accountability one perceives to have for their actions, and removes the impact these actions might otherwise have on their reputation.
With this, it is important to note, that a truly anonymous identity cannot claim ownership over a specific idea, property, or claim. Right to ownership and access is inherently impossible with an anonymous identity,
Real Identity
The other end of the spectrum is leveraging a real identity associated with a real person.
Some examples of real identities:
- Government issued id’s: Passports, birth certificates, drivers licenses not only include information about who we are, where we are from, and where we are allowed to go but also about our physical makeup, what we look like, fingerprints and even retina scans.
- Bank Accounts: In most parts of the world, the above identifications are required by law to open up a bank account. Therefore your finances are directly tied to your real identity. While your account number may be a random string of numbers, it is traced right back to your state issued id, passport, or other forms of identification.
- Facebook: many platforms such as facebook have become synonymous with a real person's identity. While it is possible to create a fake pseudonymous account, most people use their real name, a recent photo, and provide personal details such as birthdate on their social profile. This removes any level of pseudonymity on the platform and creates a direct, traceable link back to your true self.
Pseudonymous Identity
A pseudonymous identity is one in which a moniker or assigned name is used in a given context. Pseudonymous names are able to persist through time and even build reputations, right to access, and prove-ability of ownership. However, they are not directly tied to a persons real or true identity. Instead, it is indirectly associated with a real person or identity. For example, a single person can create multiple pseudo identities and keep them across various channels of communication. They provide levels of ownership while maintaining some level of privacy. Pseudonymity provides assignability while preventing character assassination.
Some examples of Pseudo Anonymity
- Twitter: People can choose to use a real identity and photo of themselves or choose to use a pseudonym. The communications are tied to and associated to the moniker or twitter handle. This builds reputation to the identity, builds followers of the identity, yet the person's real identity is never exposed. Although, the Twitter admins have access to email and/or phone number which drastically reduces the level of privacy one can hold on the platform
- Status: During account creation, you are not asked for a phone number, email, banks account or any other personally identifiable information. When an account is created, keys are generated with an associated random three-word name which effectively becomes your pseudonymous identity on the platform.
- Bitcoin & Satoshi Nakamoto: Satoshi Nakamoto is the pseudonym of the person or persons who developed bitcoin and authored the bitcoin white paper. This is a very powerful move that has had many long term impacts on Bitcoin today. Most notably, it protected the true identity of the person, or persons behind the work. If their identities had been revealed, they could have been attacked, prosecuted, and the work could have been shut down. It therefore protected the network as a whole.
Create a pseudonymous identity in Status. Available in the Playstore, App Store, and via APK.